Security Updates
This revision adds the following security updates to the stable release.
The Security Team has already released an advisory for each of these
updates:
| Advisory ID | Package |
|---|---|
| DSA-4662 | openjdk-11 |
| DSA-4734 | openjdk-11 |
| DSA-4736 | firefox-esr |
| DSA-4737 | xrdp |
| DSA-4738 | ark |
| DSA-4739 | webkit2gtk |
| DSA-4740 | thunderbird |
| DSA-4741 | json-c |
| DSA-4742 | firejail |
| DSA-4743 | ruby-kramdown |
| DSA-4744 | roundcube |
| DSA-4745 | dovecot |
| DSA-4746 | net-snmp |
| DSA-4747 | icingaweb2 |
| DSA-4748 | ghostscript |
| DSA-4749 | firefox-esr |
| DSA-4750 | nginx |
| DSA-4751 | squid |
| DSA-4752 | bind9 |
| DSA-4753 | mupdf |
| DSA-4754 | thunderbird |
| DSA-4755 | openexr |
| DSA-4756 | lilypond |
| DSA-4757 | apache2 |
| DSA-4758 | xorg-server |
| DSA-4759 | ark |
| DSA-4760 | qemu |
| DSA-4761 | zeromq3 |
| DSA-4762 | lemonldap-ng |
| DSA-4763 | teeworlds |
| DSA-4764 | inspircd |
| DSA-4765 | modsecurity |
Miscellaneous Bugfixes
This stable update adds a few important corrections to the following packages.
Note that, due to build issues, the updates for the cargo, rustc and rustc-bindgen packages are currently not available for the armel
architecture.
They may be added at a later date if the issues are resolved.
| Package | Reason |
|---|---|
| arch-test | Fix detection of s390x sometimes failing |
| asterisk | Fix crash when negotiating for T.38 with a declined stream , SIP request can change address of a SIP peer, AMI user could execute system commands, segfault in pjsip show history with IPv6 peers |
| bacula | Fix oversized digest strings allow a malicious client to cause a heap overflow in the director’s memory |
| base-files | Update /etc/debian_version for the point release |
| calamares-settings-debian | Disable displaymanager module |
| cargo | New upstream release, to support upcoming Firefox ESR versions |
| chocolate-doom | Fix missing validation |
| chrony | Prevent symlink race when writing to the PID file ; fix temperature reading |
| debian-installer | Update Linux ABI to 4.19.0-11 |
| debian-installer-netboot-images | Rebuild against proposed-updates |
| diaspora-installer | Use —frozen option to bundle install to use upstream Gemfile.lock; don’t exclude Gemfile.lock during upgrades; don’t overwrite config/oidc_key.pem during upgrades; make config/schedule.yml writeable |
| dojo | Fix prototype pollution in deepCopy method and in jqMix method |
| dovecot | Fix dsync sieve filter sync regression; fix handling of getpwent result in userdb-passwd |
| facter | Change Google GCE Metadata endpoint from v1beta1to v1 |
| gnome-maps | Fix an issue with misaligned shape layer rendering |
| gnome-shell | LoginDialog: Reset auth prompt on VT switch before fade in |
| gnome-weather | Prevent a crash when the configured set of locations are invalid |
| grunt | Use safeLoad when loading YAML files |
| gssdp | New upstream stable release |
| gupnp | New upstream stable release; prevent the CallStrangerattack ; require GSSDP 1.0.5 |
| haproxy | logrotate.conf: use rsyslog helper instead of SysV init script; reject messages where chunkedis missing from Transfer-Encoding |
| icinga2 | Fix symlink attack |
| incron | Fix cleanup of zombie processes |
| inetutils | Fix remote code execution issue |
| libcommons-compress-java | Fix denial of service issue |
| libdbi-perl | Fix memory corruption in XS functions when Perl stack is reallocated ; fix a buffer overflow on an overlong DBD class name ; fix a NULL profile dereference in dbi_profile() |
| libvncserver | libvncclient: bail out if UNIX socket name would overflow ; fix pointer aliasing/alignment issue ; limit max textchat size ; libvncserver: add missing NULL pointer checks ; fix pointer aliasing/alignment issue ; scale: cast to 64 bit before shifting ; prevent OOB accesses |
| libx11 | Fix integer overflows |
| lighttpd | Backport several usability and security fixes |
| linux | New upstream stable release; increase ABI to 11 |
| linux-latest | Update for -11 Linux kernel ABI |
| linux-signed-amd64 | New upstream stable release |
| linux-signed-arm64 | New upstream stable release |
| linux-signed-i386 | New upstream stable release |
| llvm-toolchain-7 | New upstream release, to support upcoming Firefox ESR versions; fix bugs affecting rustc build |
| lucene-solr | Fix security issue in DataImportHandler configuration handling |
| milkytracker | Fix heap overflow , stack overflow , heap overflow , use after free |
| node-bl | Fix over-read vulnerability |
| node-elliptic | Prevent malleability and overflows |
| node-mysql | Add localInfile option to control LOAD DATA LOCAL INFILE |
| node-url-parse | Fix insufficient validation and sanitization of user input |
| npm | Don’t show password in logs |
| orocos-kdl | Remove explicit inclusion of default include path, fixing issues with cmake < 3.16 |
| postgresql-11 | New upstream stable release; set a secure search_path in logical replication walsenders and apply workers ; make contrib modules’ installation scripts more secure |
| postgresql-common | Don’t drop plpgsql before testing extensions |
| pyzmq | Asyncio: wait for POLLOUT on sender in can_connect |
| qt4-x11 | Fix buffer overflow in XBM parser |
| qtbase-opensource-src | Fix buffer overflow in XBM parser ; fix clipboard breaking when timer wraps after 50 days |
| ros-actionlib | Load YAML safely |
| rustc | New upstream release, to support upcoming Firefox ESR versions |
| rust-cbindgen | New upstream release, to support upcoming Firefox ESR versions |
| ruby-ronn | Fix handling of UTF-8 content in manpages |
| s390-tools | Hardcode perl dependency instead of using ${perl:Depends}, fixing installation under debootstrap |
Step By Step tutorial to Upgrade Debian 10 to Debian 11
1. System Update
The first thing which we need to follow is ensuring that all the pre-installed packages are up to date and if any upgrade is available for them that must be installed. Open your command terminal and run the following command-
sudo apt update && sudo apt upgrade
Also, install-
sudo apt install gcc-8-base
Check System’s current version.
cat /etc/os-release
2. Replace Buster repo with Bullseye
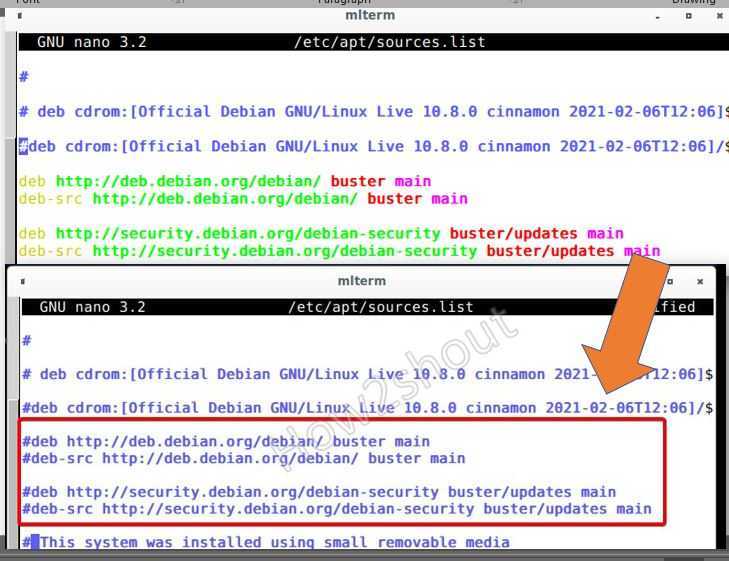
Next, we edit the source list file of Debian 10 and will replace the existing repository addresses with Debian 11 ones:
sudo nano /etc/apt/sources.list
Disable all the existing entries for Buster by adding the # sign in front of each repo link.
#deb http://deb.debian.org/debian/ buster main #deb-src http://deb.debian.org/debian/ buster main #deb http://security.debian.org/debian-security bullseye/updates main #deb-src http://security.debian.org/debian-security bullseye/updates main
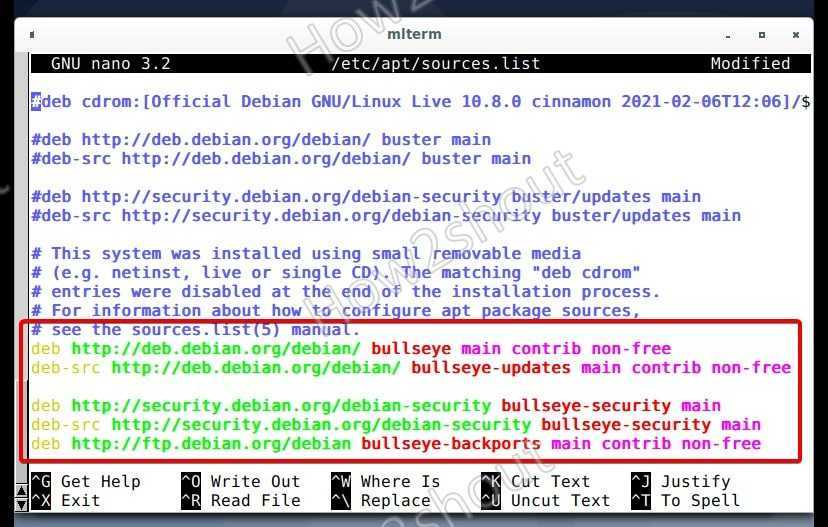
Now, at the end of the file, copy-paste the following URLs list.
deb http://deb.debian.org/debian/ bullseye main contrib non-free deb-src http://deb.debian.org/debian/ bullseye-updates main contrib non-free deb http://security.debian.org/debian-security bullseye-security main deb-src http://security.debian.org/debian-security bullseye-security main deb http://ftp.debian.org/debian bullseye-backports main contrib non-free
Save the file by pressing Crtl+X, Y, and hit the Enter key.
3. Run system update command:
To let the system recognize the newly added Repo URLs, run the system update command-
sudo apt update
If you don’t get any error after updating, then you can move further.

4. Command to full upgrade Debian 10 to 11 Linux
Finally, run the system full system upgrade command that will upgrade all the existing packages to transit your old Debian Buster system to the latest LTS Bullseye.
sudo apt full-upgrade
Follow the intermittent text wizards to set default things, when the system starts processing upgrades.
Give the system permission to download and install the required packages. Note: Make sure the system screen wouldn’t get locked while the upgrading process.
Once the Debian 10 upgrading process is completed, reboot your system.
sudo reboot
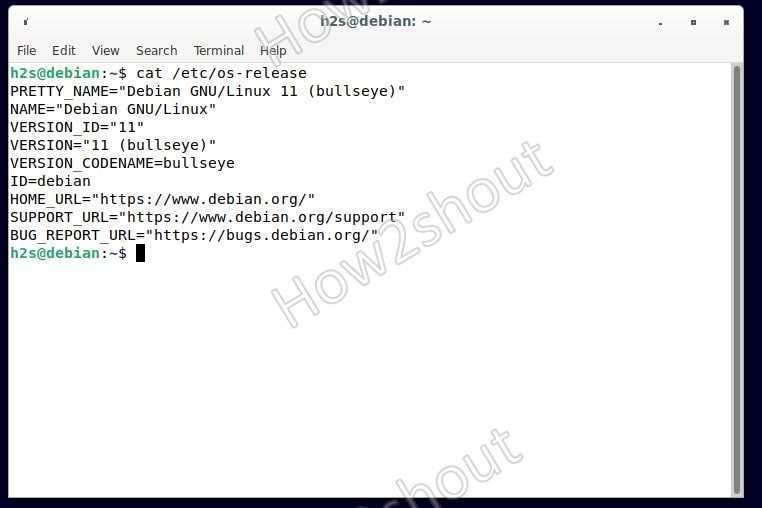
6. Check the new system version
Now, let’s check which version we have on our system now, for that run-
cat /etc/os-release
You will see the output:

Other articles-
- How to Upgrade Ubuntu 16.04 LTS to 20.04 LTS using command
- How to install Budgie Desktop on Debian
- Create Debian 11 Bullseye Bootable USB drive
Security Updates
This revision adds the following security updates to the stable release.
The Security Team has already released an advisory for each of these
updates:
| Advisory ID | Package |
|---|---|
| DSA-4766 | rails |
| DSA-4767 | mediawiki |
| DSA-4768 | firefox-esr |
| DSA-4769 | xen |
| DSA-4770 | thunderbird |
| DSA-4771 | spice |
| DSA-4772 | httpcomponents-client |
| DSA-4773 | yaws |
| DSA-4774 | linux-latest |
| DSA-4774 | linux-signed-amd64 |
| DSA-4774 | linux-signed-arm64 |
| DSA-4774 | linux-signed-i386 |
| DSA-4774 | linux |
| DSA-4775 | python-flask-cors |
| DSA-4776 | mariadb-10.3 |
| DSA-4777 | freetype |
| DSA-4778 | firefox-esr |
| DSA-4779 | openjdk-11 |
| DSA-4780 | thunderbird |
| DSA-4781 | blueman |
| DSA-4782 | openldap |
| DSA-4783 | sddm |
| DSA-4784 | wordpress |
| DSA-4785 | raptor2 |
| DSA-4786 | libexif |
| DSA-4787 | moin |
| DSA-4788 | firefox-esr |
| DSA-4789 | codemirror-js |
| DSA-4790 | thunderbird |
| DSA-4791 | pacemaker |
| DSA-4792 | openldap |
| DSA-4793 | firefox-esr |
| DSA-4794 | mupdf |
| DSA-4795 | krb5 |
| DSA-4796 | thunderbird |
| DSA-4798 | spip |
| DSA-4799 | x11vnc |
| DSA-4800 | libproxy |
Miscellaneous Bugfixes
This stable update adds a few important corrections to the following packages:
| Package | Reason |
|---|---|
| atftp | Fix denial of service issue |
| base-files | Update /etc/debian_version for the 10.8 point release |
| ca-certificates | Update Mozilla CA bundle to 2.40, blacklist expired AddTrust External Root |
| cacti | Fix SQL injection issue and stored XSS issue |
| cairo | Fix mask usage in image-compositor |
| choose-mirror | Update mirror list |
| cjson | Fix infinite loop in cJSON_Minify |
| clevis | Fix initramfs creation; clevis-dracut: Trigger initramfs creation upon installation |
| cyrus-imapd | Fix version comparison in cron script |
| debian-edu-config | Move host keytabs cleanup code out of gosa-modify-host into a standalone script, reducing LDAP calls to a single query |
| debian-installer | Use 4.19.0-14 Linux kernel ABI; rebuild against proposed-updates |
| debian-installer-netboot-images | Rebuild against proposed-updates |
| debian-installer-utils | Support partitions on USB UAS devices |
| device-tree-compiler | Fix segfault on dtc -I fs /proc/device-tree |
| didjvu | Add missing build-dependency on tzdata |
| dovecot | Fix crash when searching mailboxes containing malformed MIME messages |
| dpdk | New upstream stable release |
| edk2 | CryptoPkg/BaseCryptLib: fix NULL dereference |
| emacs | Don’t crash with OpenPGP User IDs with no e-mail address |
| fcitx | Fix input method support in Flatpaks |
| file | Increase name recursion depth to 50 by default |
| geoclue-2.0 | Check the maximum allowed accuracy level even for system applications; make the Mozilla API key configurable and use a Debian-specific key by default; fix display of the usage indicator |
| gnutls28 | Fix test suite error caused by expired certificate |
| grub2 | When upgrading grub-pc noninteractively, bail out if grub-install fails; explicitly check whether the target device exists before running grub-install; grub-install: Add backup and restore; don’t call grub-install on fresh install of grub-pc |
| highlight.js | Fix prototype pollution |
| intel-microcode | Update various microcode |
| iproute2 | Fix bugs in JSON output; fix race condition that DOSes the system when using ip netns add at boot |
| irssi-plugin-xmpp | Do not trigger the irssi core connect timeout prematurely, thus fixing STARTTLS connections |
| libdatetime-timezone-perl | Update for new tzdata version |
| libdbd-csv-perl | Fix test failure with libdbi-perl 1.642-1+deb10u2 |
| libdbi-perl | Security fix |
| libmaxminddb | Fix heap-based buffer over-read |
| lttng-modules | Fix build on kernel versions >= 4.19.0-10 |
| m2crypto | Fix compatibility with OpenSSL 1.1.1i and newer |
| mini-buildd | builder.py: sbuild call: set ‘—no-arch-all’ explicitly |
| net-snmp | snmpd: Add cacheTime and execType flags to EXTEND-MIB |
| node-ini | Do not allow invalid hazardous string as section name |
| node-y18n | Fix prototype pollution issue |
| nvidia-graphics-drivers | New upstream release; fix possible denial of service and information disclosure |
| nvidia-graphics-drivers-legacy-390xx | New upstream release; fix possible denial of service and information disclosure |
| pdns | Security fixes |
| pepperflashplugin-nonfree | Turn into a dummy package taking care of removing the previously installed plugin (no longer functional nor supported) |
| pngcheck | Fix buffer overflow |
| postgresql-11 | New upstream stable release; security fixes |
| postsrsd | Ensure timestamp tags aren’t too long before trying to decode them |
| python-bottle | Stop allowing ;as a query-string separator |
| python-certbot | Automatically use ACMEv2 API for renewals, to avoid issues with ACMEv1 API removal |
| qxmpp | Fix potential SEGFAULT on connection error |
| silx | python(3)-silx: Add dependency on python(3)-scipy |
| slirp | Fix buffer overflows |
| steam | New upstream release |
| systemd | journal: do not trigger assertion when journal_file_close() is passed NULL |
| tang | Avoid race condition between keygen and update |
| tzdata | New upstream release; update included timezone data |
| unzip | Apply further fixes for CVE-2019-13232 |
| wireshark | Fix various crashes, infinite loops and memory leaks |
























